Manually Generating Ssh Keys In Mac
3 days ago I use something specific to the company for who I’m adding the key. You can see here the new SSH key is examplecomidrsa. Please be careful here, if you leave the default you may overwrite your existing key. You probably don’t want to do that. The Key is the Config. Head on over to where your SSH keys are stored, probably in /.ssh directory. Dec 02, 2019 Once the key pair is generated, the next step is to put the public SSH key on the remote server. Depending on your setup, this can be done by entering a couple commands in the terminal window, using JumpCloud, or by manually placing the public SSH key on the remote server (DigitalOcean). Behind the Scenes of SSH Key Authentication. To use SSH keys with your Droplets, you need to: Create an SSH key using an SSH client installed on your local computer. OpenSSH is included on Linux, macOS, and Windows Subsystem for Linux. Windows users without Bash can use PuTTY. Add your SSH key to your Droplets. An SSH key consists of a pair of files. One is the private key, which you should never give to anyone. No one will ever ask you for it and if so, simply ignore them - they are trying to steal it. The other is the public key. When you generate your keys, you will use ssh-keygen to store the keys in a safe location so you can authenticate with.
- Manually Generating Ssh Keys In Mac Free
- What Are Ssh Keys
- Manually Generating Ssh Keys In Mac Free
- Mac Ssh Key Location
Connect to a server by using SSH on Linux or Mac OS X
This article provides steps for connecting to a cloud server froma computer running Linux® or MacOS® X by using Secure Shell (SSH).It also discusses generating an SSH key and adding a public key tothe server.
Introduction
SSH is a protocol through which you can access your cloud server and runshell commands. You can use SSH keys to identify trusted computers withoutthe need for passwords and to interact with your servers.
SSH is encrypted with Secure Sockets Layer (SSL), which makes it difficultfor these communications to be intercepted and read.
Note: Many of the commands in this article must be run on your localcomputer. The default commands listed are for the Linux command line orMacOS X Terminal. To make SSH connections from Windows®, you can use a clientsimilar to the free program, PuTTY.To generate keys, you can use a related program, PuTTYGen.
Log in
Manually Generating Ssh Keys In Mac Free
Using the Internet Protocol (IP) address and password for your cloud server, log in byrunning the following ssh command with username@ipaddress as the argument:
The system prompts you to enter the password for the account to which you’reconnecting.
Remote host identification
If you rebuilt your cloud server, you might get the following message:
One of the security features of SSH is that when you log in to a cloudserver, the remote host has its own key that identifies it. When you tryto connect, your SSH client checks the server’s key against any keysthat it has saved from previous connections to that IP address. After yourebuild a cloud server, that remote host key changes, so your computerwarns you of possibly suspicious activity.
yes/no: yesThen try generating a new RSA keypair anew:configure terminalcrypto key generate rsa label ssh modulus 1024The name for the keys will be: ssh% The key modulus size is 1024 bits% Generating 1024 bit RSA keys, keys will be non-exportable.OK (elapsed time was 3 seconds)This alone should make sure that the SSH is able to run in SSHv2. Hmm, this is an interesting issue. Perhaps you have several RSA keypairs configured, and the SSH is using some short keypair that does not allow running SSHv2.I suggest erasing all existing RSA keypairs using the crypto key zeroize rsa as follows:configure terminalcrypto key zeroize rsa% All RSA keys will be removed.% All router certs issued using these keys will also be removed.Do you really want to remove these keys? In addition, I have given the keypair a special name that can be used to select it in diverse applications. Using rsa keys generated from 4500 switch diagram.
To ensure the security of your server, you canuse the web console in the Cloud Control Panel to verify your server’s new key.If you’re confident that you aren’t being spoofed, you can skip thatstep and delete the record of the old SSH host key as follows:
On your local computer, edit the SSH known_hosts file and remove anylines that start with your cloud server’s IP address.
Note: Use the editor of your choice, such as nano on Debian or theUbuntu operating systemor vi on RPM or CENTOS servers. For simplicity, this article just uses nano. If you prefer to use vi,substitute vi for nano in the edit commands.For more on using nano, seehttps://support.rackspace.com/how-to/modify-your-hosts-file/.
If you are not using Linux or MacOS X on your local computer, thelocation of the known_hosts file might differ. Refer to your OS forinformation about the file location. PuTTY on Windows gives you theoption to replace the saved host key.
Generate a new SSH key pair
You can secure SSH access to your cloud server against brute forcepassword attacks by using a public-private key pair. A public key is placed onthe server and a matching private key is placed on your local computer. If youconfigure SSH on your server to accept only connections using keys,then no one can log in by using just a password. Connecting clientsare required to use a private key that has a public key registered onthe server. For more on security, reviewLinux server security best practices.
Use the following steps to generate an SSH key pair:
Run the following command using your email address as a label.Substitute your email address for
your_email@example.cominthe command.A message indicates that your public-private RSA key pair isbeing generated.
At the prompt, press Enter to use the default location or entera file in which to save the key and press Enter.
If you want the additional security of a password for the key pair,enter a passphraseand press Enter. If you don’t want to use a passwordwith the key pair, press Enter to continue without setting one.
Your key pair is generated, and the output looks similar to the following example:
Optionally, add your new key to the local ssh-agent file to enableSSH to find your key without the need to specify its location everytime that you connect:
You can use an SSH configuration shortcut instead of the ssh-agent fileby following the instructions in the Shortcut configuration sectionlater in this article.
Add the public key to your cloud account
To make it easy to add your key to new cloud servers that you create,upload the public key to your cloud account by following these steps:
- Log in to the Cloud Control Panel.
- In the top navigation bar, click Select a Product > Rackspace Cloud.
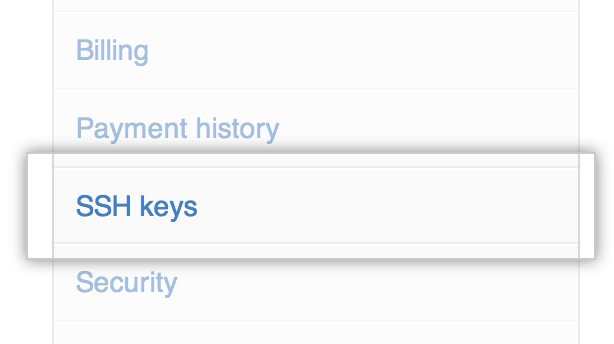
- Select Servers > SSH Keys.
- Click Add Public Key.
- Enter a key name, such as Work Laptop, to remind you which computer this key is for.
- Select the region for which you want to store the public key. Tostore your key in multiple regions, repeat these steps foreach region. The key must reside in the same region as the server.
Paste the contents of the id_rsa.pub file that you created intothe Public Key field. You can get the file contents by eitheropening the file in a text editor or by running the followingcommand:
- Click Add Public Key.
If you want to add the key manually, instead of by using the Control Panel, reviewLinux server security best practicesand use the following command:
Create a new server by using a stored key
What Are Ssh Keys
When you create a new cloud server, you can add a stored key to the newserver.
However, I want to use privatekey to encrypt some string, generate USERCERTIFICATION, and use publickey for users to decrypt it and get the string. Crypto key generate rsa modulus 1024 invalid input. I have the n, d, e for RSA algorithm.
On the Create Server page, expand the Advanced Options section.
From the SSH Key menu, select your key from the list.
If you don’t see a stored key in the list, you can perform one of the following actions:
- Switch the region for the new server to the region where you have stored the SSH key.
- Repeat the steps in the preceding section, Add the public key to your cloud account,to add the key to the region in which you want to create the new server.
Add the key to an existing server
You can’t use the Cloud Control Panel to add a public key to anexisting server. Follow these steps to add the key manually:
On your cloud server, create a directory named .ssh in the homefolder of the user that you connect to by using SSH.
Create or edit the authorized_keys file and add your public key tothe list of authorized keys by using the following command:
A key is all on one line, so ensure that the key isn’t broken byline breaks. You can have multiple keys in the authorized_keysfile, with one key per line.
Set the correct permissions on the key by using the following commands:
If you have any issues and need to fix permissions issues, run the following comand:
After you have added the public key to the authorized_keys, you can make an SSHconnection by using your key pair instead of the account password.
Shortcut configuration
Use the following instructions to set up a connection shortcut by creating a~/.ssh/config file on your local computer and adding your server and keydetails to it.
Using a text editor, add the following text to the ~/.ssh/config file, changing thevalues to match your server information:
Each of the following entries describes a feature of the server:
- Host: A shortcut name that you use to tell SSH to use thisconnection.
- HostName: The address of the server to which you connect.
- User: The name of the user account to connect to on theserver.
- IdentityFile: The location of the private key file (id_rsa).
After you set up the config file, connect to the server by usingthe following command with your shortcut name:
Troubleshooting
Manually Generating Ssh Keys In Mac Free
If you have trouble making a new connection after you restart theserver, use the following steps to help you resolve the issue:
Mac Ssh Key Location
The best way to troubleshoot SSH or SFTP login issues is to attempt tologin through SSH while logged into the Emergency Console and to watch the log,which typically includes the reason for a failure. If no reason is given,it could be a firewall issue. For RPM servers, run the following command to watch the log:
For Debian servers, run the following command to watch the log:
- If you get a
connection timeouterror, check the IP address thatyou used to ensure that it’s correct. You might also check theserver’s iptables to ensure that it isn’t blocking the port used by SSH. - If you get a
connection refusederror, you might be trying to useSSH with the wrong port. If you changed your server to listen to aport other than 22, use the-poption with SSH to specifythe port. - If your login is rejected, then you might have an issuewith your key. Change the
sshdconfiguration to allow passwordconnections by settingPasswordAuthenticationtoyes. Restartthe server and try again. If you connect after these changes, thenthe issue is with the key and you must verify that the key is in theright place on the server. If all else fails, review your changes and restart the SSH daemon onthe server by running the following command:
If you get a message that the SSH service is unknown, run thecommand with
sshdas the service name instead.
Experience what Rackspace has to offer.
©2020 Rackspace US, Inc.
Except where otherwise noted, content on this site is licensed under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported License